Panduan ini membantu Anda memahami dampak dan perubahan yang diperlukan pada add-on Anda yang diperkenalkan oleh Chrome yang mengakhiri dukungan untuk cookie pihak ketiga.
Ringkasan
Pada 4 Januari 2024, Chrome memperkenalkan Fitur Anti-Pelacakan, yang membatasi akses situs ke cookie pihak ketiga (3P) secara default, untuk 1% pengguna. Pada awal tahun 2025, Chrome diperkirakan akan menghentikan penggunaan cookie pihak ketiga sepenuhnya.
Setidaknya ada dua perjalanan pengguna yang terpengaruh di add-on Classroom:
- Alur Single Sign-On (SSO) Google
- Membuka pengguna ke tab baru
SSO Google
Selama alur SSO Google, pengguna akan diarahkan ke dialog untuk login ke Akun Google mereka dan menyetujui berbagi data.
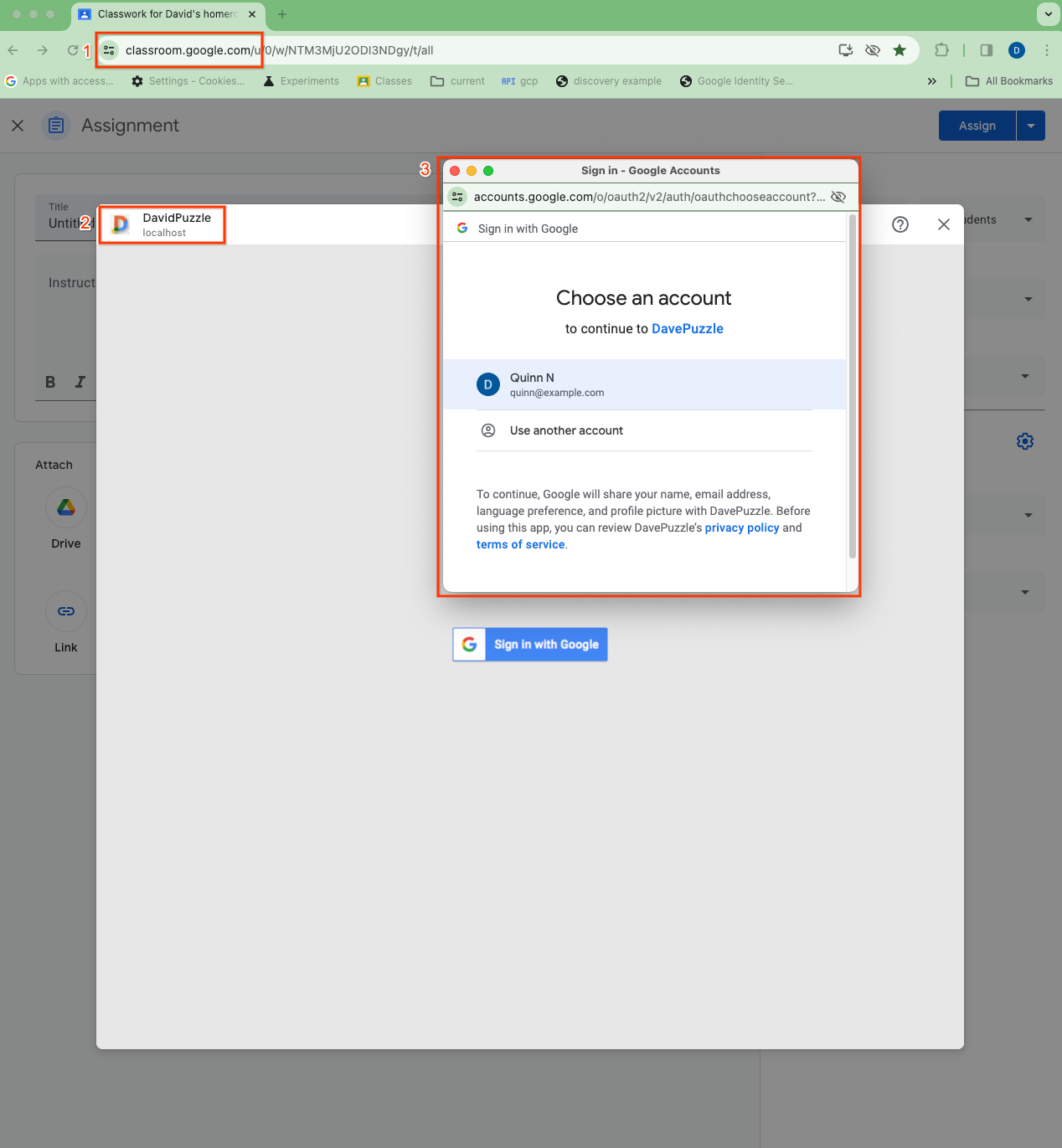
Gambar 1. Visualisasi tiga konteks cookie yang berbeda selama SSO dari dalam iframe: (1) aplikasi Classroom tingkat atas, (2) iframe sematan pihak ketiga (DavidPuzzle di localhost dalam kasus ini), dan (3) dialog OAuth tingkat atas.
Dalam penerapan add-on yang umum, cookie sesi ditetapkan setelah proses login ini selesai. IFrame add-on, yang berada dalam konteks sematan, dimuat ulang, kini dengan cookie sesi, sehingga pengguna dapat mengakses sesi yang diautentikasi. Namun, jika cookie pihak ketiga dinonaktifkan, situs dalam konteks sematan seperti iframe add-on tidak dapat mengakses cookie dari konteks level teratas masing-masing. Untuk add-on Classroom, pengguna tidak dapat mengakses sesi yang diautentikasi dan terjebak dalam loop login.
Untuk penerapan yang menetapkan cookie sesi dalam konteks iframe sematan, masalah ini dapat diatasi dengan CHIPS API, yang memungkinkan situs sematan menetapkan dan mengakses cookie yang dipartisi (cookie yang diberi kunci pada domain penyemat dan sematan). Namun, penerapan yang menetapkan cookie sesi dalam konteks tingkat teratas dialog login tidak dapat mengakses cookie tanpa partisi dalam iframe, sehingga mencegah login.
Tab baru
Karena alasan serupa, jika pengguna memiliki sesi yang diautentikasi berbasis cookie di iframe add-on, dan iframe meluncurkan pengguna ke tab tingkat teratas baru untuk aktivitas, tab tingkat teratas tidak dapat mengakses cookie sesi yang dipartisi dari iframe. Hal ini mencegah status sesi iframe tetap ada di aktivitas tab baru dan mungkin memaksa pengguna untuk login lagi di tab baru, misalnya. CHIPS API tidak dapat menyelesaikan masalah ini, berdasarkan desain; cookie iframe yang dipartisi tidak dapat diakses dalam konteks tingkat teratas.
Tindakan developer
Ada beberapa tindakan yang harus Anda pertimbangkan untuk memastikan add-on Anda terus berfungsi sebagaimana mestinya saat Chrome menghentikan penggunaan cookie pihak ketiga.
- Periksa penggunaan cookie pihak ketiga dalam perjalanan penting pengguna add-on Anda. Lebih khusus lagi, lakukan pengujian dengan cookie pihak ketiga dinonaktifkan untuk mengevaluasi dampak pada penerapan spesifik Anda.
Jelajahi Storage Access API. Untuk semua penerapan add-on, sebaiknya Anda mempelajari Storage Access API (SAA) Storage Access. SAA memungkinkan iframe untuk mengakses cookie di luar konteks iframe. SAA tersedia di Chrome hari ini, dan didukung oleh aplikasi Classroom.
Ikut serta dalam FedCM. Selain itu, jika Anda menggunakan GIS, library Login dengan Google, panduan resmi dari tim Identitas adalah mengaktifkan FedCM. Hal ini tidak menggantikan kemampuan cookie pihak ketiga, tetapi pada akhirnya akan diperlukan di GIS sebagai bagian dari penghentian penggunaan cookie pihak ketiga. FedCM tersedia di Chrome saat ini dan didukung di Classroom, tetapi perilaku dan fiturnya masih dalam pengembangan dan terbuka untuk menerima masukan.
Bermigrasi ke GIS. Jika Anda menggunakan library GSIv2 yang tidak digunakan lagi, yang juga dikenal sebagai library Login dengan Google, sebaiknya bermigrasi ke GIS, karena dukungan untuk GSIv2 ke depannya tidak jelas.
Ajukan permohonan penundaan uji coba penghentian penggunaan. Chrome menawarkan uji coba penghentian penggunaan untuk memungkinkan kasus penggunaan non-iklan menunda efek penghentian penggunaan cookie pihak ketiga. Jika disetujui, Anda akan diberi token yang dapat digunakan di add-on untuk mengaktifkan cookie pihak ketiga bagi asal Anda hingga tahun 2024, sekaligus bermigrasi ke solusi jangka panjang seperti SAA. Setelah menerapkan, Anda akan diminta untuk memberikan ID atau link bug untuk laporan kerusakan. Tim kami telah mengajukan masalah ini untuk add-on Classroom dan Anda dapat memberikan bug ini.