OAuth bağlantısı türü, iki endüstri standardı OAuth 2.0 akışını (dolaylı ve yetkilendirme kodu akışları) destekler.
Dolaylı kod akışında Google, yetkilendirme uç noktanızı kullanıcının tarayıcısında açar. Başarılı bir şekilde oturum açtıktan sonra Google'a uzun ömürlü bir erişim jetonu döndürürsünüz. Bu erişim jetonu artık Asistan'dan Action'ınıza gönderilen her isteğe dahil edilir.
Yetkilendirme kodu akışında iki uç noktaya ihtiyacınız vardır:
- Oturum açma kullanıcı arayüzünü henüz oturum açmamış kullanıcılara sunmaktan ve istenen erişime kısa süreli bir yetkilendirme kodu biçiminde izin kaydetmekten sorumlu olan yetkilendirme uç noktası.
- İki tür exchange'den sorumlu olan jeton değişimi uç noktası:
- Yetkilendirme kodunu uzun ömürlü yenileme jetonu ve kısa ömürlü erişim jetonu ile değiştirir. Bu değişim, kullanıcı hesap bağlama akışından geçer.
- Kısa ömürlü bir erişim jetonu için uzun süreli yenileme jetonunu değiştirir. Bu exchange, Google'ın süresi dolmuş olduğundan yeni bir erişim jetonuna ihtiyacı olduğunda gerçekleşir.
Örtülü akış kullanılarak verilen erişim jetonlarının geçerlilik süresinin hiçbir zaman dolmaması, Google'ın örtülü akışla kullanılması nedeniyle kullanıcının hesabını tekrar bağlamayı zorunlu kıldığı için Google, örtülü akış akışının uygulanmasını önerir. Güvenlik nedeniyle jetonun süresinin dolması gerekiyorsa kimlik doğrulama kodu akışını kullanmanız önerilir.
OAuth hesap bağlamayı uygulama
Projeyi yapılandırma
Projenizi OAuth bağlantısı kullanacak şekilde yapılandırmak için aşağıdaki adımları uygulayın:
- Actions Console'u açın ve kullanmak istediğiniz projeyi seçin.
- Geliştir sekmesini tıklayın ve Hesap bağlama'yı seçin.
- Hesap bağlama'nın yanındaki anahtarı etkinleştirin.
- Hesap oluşturma bölümünde Hayır, yalnızca web sitemde hesap oluşturulmasına izin vermek istiyorum'u seçin.
Bağlantı türü bölümünde OAuth ve Yetkilendirme kodu'nu seçin.
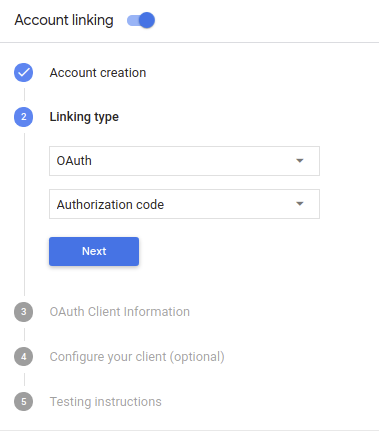
Müşteri Bilgileri bölümünde:
- Google'dan gelen istekleri tanımlamak için Google'a yönelik İşlemleriniz tarafından verilen istemci kimliği özelliğine bir değer atayın.
- Google tarafından İşlemlerinize verilen istemci kimliğinin değerini not edin;
- Yetkilendirme ve Jeton Değişimi uç noktalarınızın URL'lerini ekleyin.
- Kaydet'i tıklayın.
OAuth sunucunuzu uygulama
An OAuth 2.0 server implementation of the authorization code flow consists of two endpoints, which your service makes available by HTTPS. The first endpoint is the authorization endpoint, which is responsible for finding or obtaining consent from users for data access. The authorization endpoint presents a sign-in UI to your users that aren't already signed in and records consent to the requested access. The second endpoint is the token exchange endpoint, which is used to obtain encrypted strings called tokens that authorize the Action user to access your service.
When your Action needs to call one of your service's APIs, Google uses these endpoints together to get permission from your users to call these APIs on their behalf.
OAuth 2.0 auth code flow session initiated by Google has the following flow:
- Google opens your authorization endpoint in the user's browser. If the flow started on a voice-only device for an Action, Google would transfer the execution to a phone.
The user signs in (if not signed in already) and grants Google permission to access their data with your API if they haven't already granted permission.
Your service creates an authorization code and returns it to Google by redirecting the user's browser back to Google with the authorization code attached to the request.
Google sends the authorization code to your token exchange endpoint, which verifies the authenticity of the code and returns an access token and a refresh token. The access token is a short-lived token that your service accepts as credentials to access APIs. The refresh token is a long-lived token that Google can store and use to acquire new access tokens when they expire.
After the user has completed the account linking flow, every subsequent request sent from the Assistant to your fulfillment webhook contains an access token.
Handle authorization requests
When your Action needs to perform account linking via an OAuth 2.0 authorization code flow, Google sends the user to your authorization endpoint with a request that includes the following parameters:
| Authorization endpoint parameters | |
|---|---|
client_id |
The Google client ID you registered with Google. |
redirect_uri |
The URL to which you send the response to this request. |
state |
A bookkeeping value that is passed back to Google unchanged in the redirect URI. |
scope |
Optional: A space-delimited set of scope strings that specify the data Google is requesting authorization for. |
response_type |
The string code. |
For example, if your authorization endpoint is available at https://myservice.example.com/auth,
a request might look like:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&scope=REQUESTED_SCOPES&response_type=code
For your authorization endpoint to handle sign-in requests, do the following steps:
Verify that the
client_idmatches the Google client ID you registered with Google, and that theredirect_urimatches the redirect URL provided by Google for your service. These checks are important to prevent granting access to unintended or misconfigured client apps.If you support multiple OAuth 2.0 flows, also confirm that the
response_typeiscode.Check if the user is signed in to your service. If the user isn't signed in, complete your service's sign-in or sign-up flow.
Generate an authorization code that Google will use to access your API. The authorization code can be any string value, but it must uniquely represent the user, the client the token is for, and the code's expiration time, and it must not be guessable. You typically issue authorization codes that expire after approximately 10 minutes.
Confirm that the URL specified by the
redirect_uriparameter has the following form:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
Redirect the user's browser to the URL specified by the
redirect_uriparameter. Include the authorization code you just generated and the original, unmodified state value when you redirect by appending thecodeandstateparameters. The following is an example of the resulting URL:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID?code=AUTHORIZATION_CODE&state=STATE_STRING
Handle token exchange requests
Your service's token exchange endpoint is responsible for two kinds of token exchanges:
- Exchange authorization codes for access tokens and refresh tokens
- Exchange refresh tokens for access tokens
Token exchange requests include the following parameters:
| Token exchange endpoint parameters | |
|---|---|
client_id |
A string that identifies the request origin as Google. This string must be registered within your system as Google's unique identifier. |
client_secret |
A secret string that you registered with Google for your service. |
grant_type |
The type of token being exchanged. Either
authorization_code or refresh_token. |
code |
When grant_type=authorization_code, the code Google
received from either your sign-in or token exchange endpoint. |
redirect_uri |
When grant_type=authorization_code, this parameter is the
URL used in the initial authorization request. |
refresh_token |
When grant_type=refresh_token, the refresh token Google
received from your token exchange endpoint. |
Exchange authorization codes for access tokens and refresh tokens
After the user signs in and your authorization endpoint returns a short-lived authorization code to Google, Google sends a request to your token exchange endpoint to exchange the authorization code for an access token and a refresh token.
For these requests, the value of grant_type is authorization_code, and the value
of code is the value of the authorization code you previously granted to Google.
The following is an example of a request to exchange an authorization code for an
access token and a refresh token:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded client_id=GOOGLE_CLIENT_ID&client_secret=GOOGLE_CLIENT_SECRET&grant_type=authorization_code&code=AUTHORIZATION_CODE&redirect_uri=REDIRECT_URI
To exchange authorization codes for an access token and a refresh token, your
token exchange endpoint responds to POST requests executing the following steps:
- Verify that the
client_ididentifies the request origin as an authorized origin, and that theclient_secretmatches the expected value. - Verify the following:
- The authorization code is valid and not expired, and the client ID specified in the request matches the client ID associated with the authorization code.
- The URL specified by the
redirect_uriparameter is identical to the value used in the initial authorization request.
- If you cannot verify all of the above criteria, return an HTTP
400 Bad Request error with
{"error": "invalid_grant"}as the body. - Otherwise, using the user ID from the authorization code, generate a refresh token and an access token. These tokens can be any string value, but they must uniquely represent the user and the client the token is for, and they must not be guessable. For access tokens, also record the expiration time of the token (typically an hour after you issue the token). Refresh tokens do not expire.
- Return the following JSON object in the body of the HTTPS response:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "refresh_token": "REFRESH_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
Google stores the access token and the refresh token for the user and records the expiration of the access token. When the access token expires, Google uses the refresh token to get a new access token from your token exchange endpoint.
Exchange refresh tokens for access tokens
When an access token expires, Google sends a request to your token exchange endpoint to exchange a refresh token for a new access token.
For these requests, the value of grant_type is refresh_token, and the value
of refresh_token is the value of the refresh token you previously granted to Google.
The following is an example of a request to exchange a refresh token for an
access token:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded client_id=GOOGLE_CLIENT_ID&client_secret=GOOGLE_CLIENT_SECRET&grant_type=refresh_token&refresh_token=REFRESH_TOKEN
To exchange a refresh token for an access token, your token exchange endpoint
responds to POST requests executing the following steps:
- Verify that the
client_ididentifies the request origin as Google, and that theclient_secretmatches the expected value. - Verify that the refresh token is valid, and that the client ID specified in the request matches the client ID associated with the refresh token.
- If you cannot verify all of the above criteria, return an HTTP
400 Bad Request error with
{"error": "invalid_grant"}as the body. - Otherwise, use the user ID from the refresh token to generate an access token. These tokens can be any string value, but they must uniquely represent the user and the client the token is for, and they must not be guessable. For access tokens, also record the expiration time of the token (typically an hour after you issue the token).
- Return the following JSON object in the body of the HTTPS
response:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
Kimlik doğrulama akışı için sesli kullanıcı arayüzünü tasarlama
Kullanıcının doğrulanıp doğrulanmadığını kontrol edin ve hesap bağlama akışını başlatın.
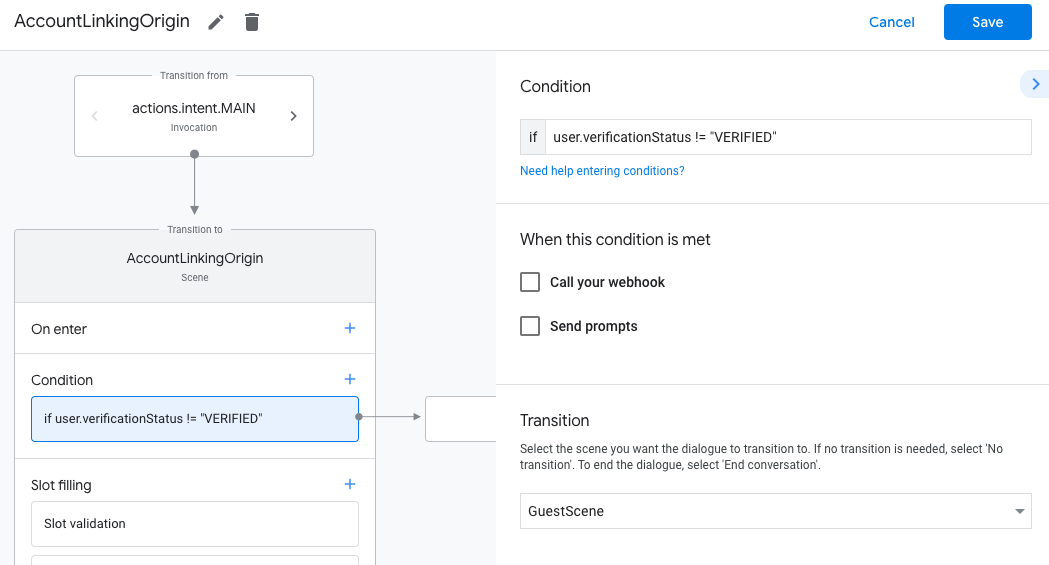
- Actions Builder projenizi Actions Console'da açın.
- İşleminizde hesap bağlama işlemini başlatmak için yeni bir sahne oluşturun:
- Sahneler'i tıklayın.
- Yeni bir sahne eklemek için ekle (+) simgesini tıklayın.
- Yeni oluşturulan sahnede, Koşullar için ekle simgesini add tıklayın.
- Sohbetle ilişkili kullanıcının doğrulanmış bir kullanıcı olup olmadığını kontrol eden bir koşul ekleyin. Kontrol başarısız olursa İşleminiz, görüşme sırasında hesap bağlama işlemini gerçekleştiremez ve hesap bağlama gerektirmeyen işlevlere erişim sağlamaya geri dönmelidir.
- Koşul bölümündeki
Enter new expressionalanına aşağıdaki mantığı girin:user.verificationStatus != "VERIFIED" - Geçiş bölümünde, hesap bağlama gerektirmeyen veya yalnızca konuklara özel işlevlerin giriş noktası olan bir sahne seçin.
- Koşul bölümündeki
- Koşullar için ekle simgesini add tıklayın.
- Kullanıcının ilişkili bir kimliği yoksa hesap bağlama akışını tetikleyecek bir koşul ekleyin.
- Koşul bölümündeki
Enter new expressionalanına aşağıdaki mantığı girin:user.verificationStatus == "VERIFIED" - Geçiş bölümünde Hesap Bağlama sistem sahnesini seçin.
- Kaydet'i tıklayın.
- Koşul bölümündeki
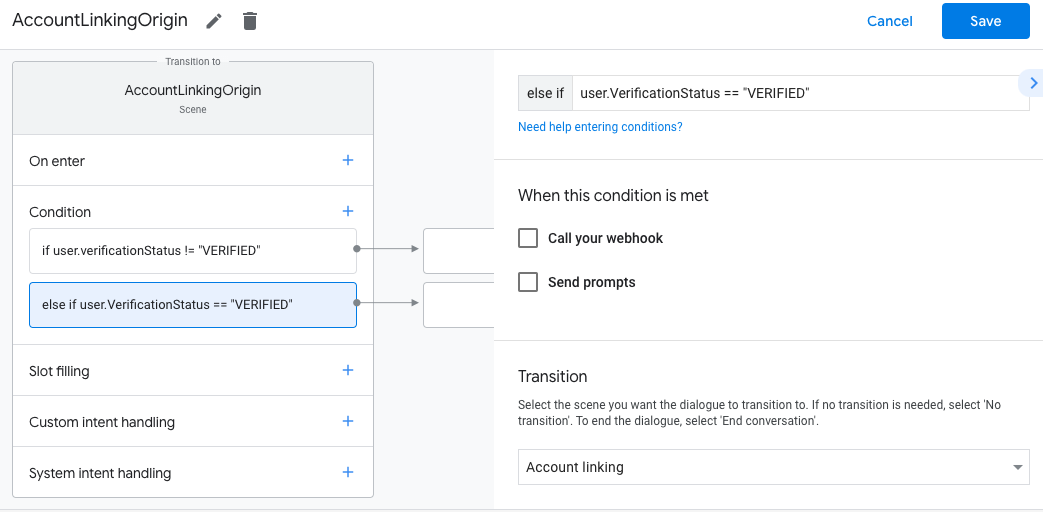
Kaydettikten sonra projenize <SceneName>_AccountLinking adlı yeni bir hesap bağlama sistemi sahnesi eklenir.
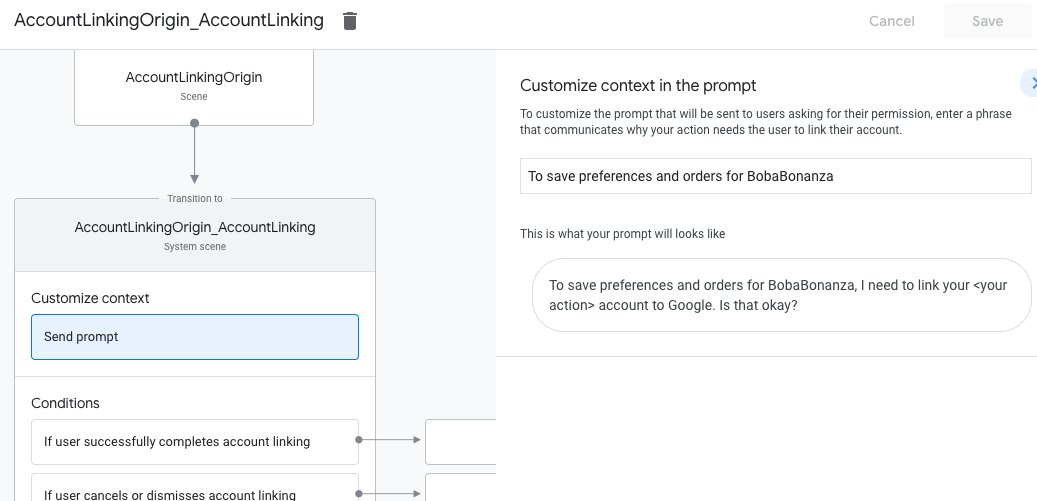
Hesap bağlama sahnesini özelleştirme
- Sahneler bölümünde hesap bağlama sistemi sahnesini seçin.
- İstemi gönder'i tıklayın ve kullanıcıya İşlem'in kimliğine neden erişmesi gerektiğini açıklayan kısa bir cümle ekleyin (örneğin, "Tercihlerinizi kaydetmek için").
- Kaydet'i tıklayın.
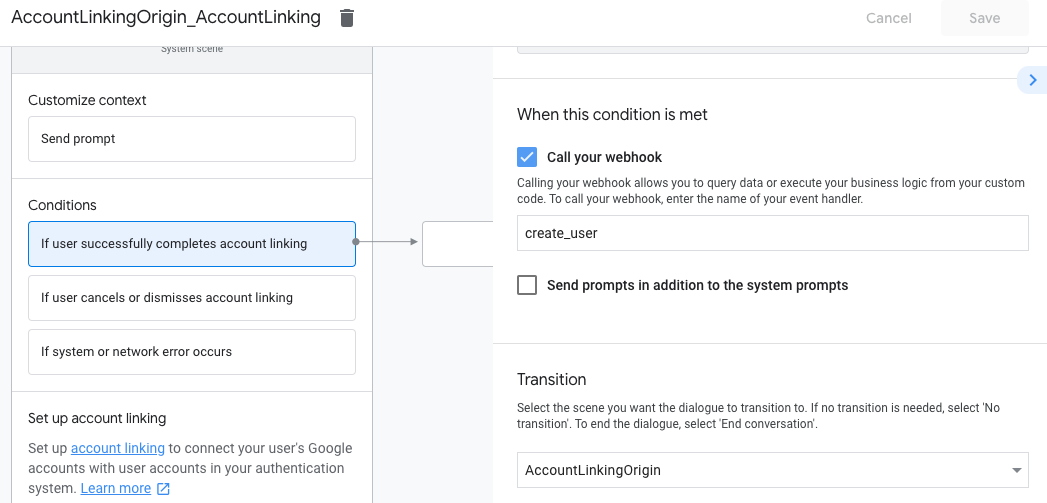
- Koşullar bölümünde Kullanıcı hesap bağlama işlemini başarıyla tamamlarsa'yı tıklayın.
- Kullanıcı hesabını bağlamayı kabul ederse akışın nasıl devam edeceğini yapılandırın. Örneğin, gerekli özel işletme mantığını işlemek ve başlangıç sahnesine geri dönmek için webhook'u çağırın.
- Kaydet'i tıklayın.
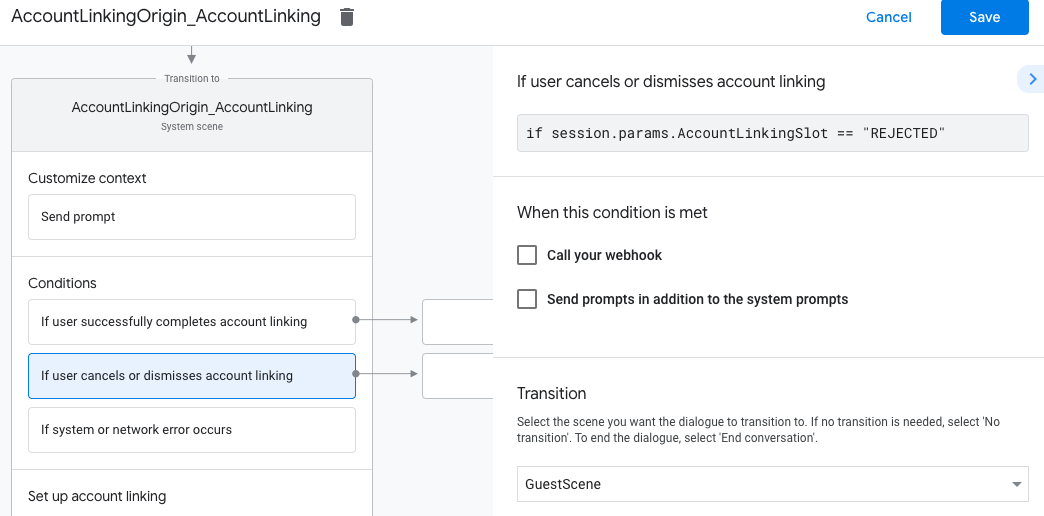
- Koşullar bölümünde Kullanıcı hesap bağlantısını iptal ederse veya kapatırsa'yı tıklayın.
- Kullanıcı hesabını bağlamayı kabul etmezse akışın nasıl devam edeceğini yapılandırın. Örneğin, onay mesajı gönderin ve hesap bağlama gerektirmeyen işlevler sunan sahnelere yönlendirin.
- Kaydet'i tıklayın.
- Koşullar bölümünde Sistem veya ağ hatası oluşursa'yı tıklayın.
- Hesap bağlama akışı, sistem veya ağ hataları nedeniyle tamamlanamazsa akışın nasıl devam edeceğini yapılandırın. Örneğin, onay mesajı gönderin ve hesap bağlama gerektirmeyen işlevler sunan sahnelere yönlendirin.
- Kaydet'i tıklayın.
Veri erişimi isteklerini ele alma
Asistan isteği erişim jetonu içeriyorsa, önce erişim jetonunun geçerli (ve süresinin dolmamış) olup olmadığını kontrol edin, ardından ilişkili kullanıcı hesabını veritabanınızdan alın.