OAuth 关联类型支持两种业界标准 OAuth 2.0 流程,即隐式和授权代码流程。
在隐式代码流程中,Google 会在用户浏览器中打开您的授权端点。成功登录后,系统会向 Google 返回长期访问令牌。现在,从 Google 助理向你的 Action 发送的每个请求中都包含此访问令牌。
在授权代码流程中,您需要两个端点:
- 授权端点,该端点负责向尚未登录的用户显示登录界面,并以短期授权代码的形式记录所请求的访问。
- 令牌交换端点,负责两种类型的交换:
- 将授权代码交换为长期刷新令牌和短期访问令牌。用户完成帐号关联流程后,系统会进行这种交换。
- 将长期刷新令牌换成短期访问令牌。Google 需要新访问令牌时,由于此令牌已过期,因此会进行此交换。
虽然隐式代码流程的实现更简单,但 Google 建议通过隐式流程发出的访问令牌永远不会过期,因为将令牌过期与隐式流程一起使用会强制用户再次关联其帐号。如果出于安全考虑需要令牌到期,强烈建议您考虑使用身份验证代码流程。
实现 OAuth 账号关联
配置项目
如需将项目配置为使用 OAuth 关联,请按以下步骤操作:
- 打开 Actions 控制台,然后选择要使用的项目。
- 点击开发标签页,然后选择账号关联。
- 启用账号关联旁边的开关。
- 在账号创建部分,选择否,我只想允许在我的网站上创建账号。
在关联类型中,选择 OAuth 和隐式。
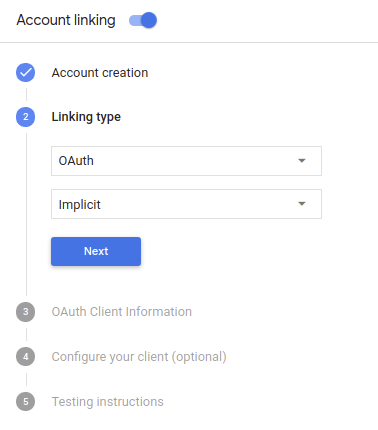
在客户信息中:
- 为 Actions 发给 Google 的客户端 ID 赋值,以标识来自 Google 的请求。
- 插入授权端点和令牌交换端点的网址。
- 点击保存。
实现 OAuth 服务器
为了支持 OAuth 2.0 隐式流程,您的服务会进行授权 端点。此端点负责 就数据访问征得用户同意。授权端点 向尚未登录的用户显示登录界面,并记录 同意所请求的访问。
当您的 Action 需要调用您的某项授权的 API 时,Google 会使用 此端点来获得用户许可,以在其上调用这些 API 。
由 Google 发起的典型 OAuth 2.0 隐式流会话具有以下特征: 以下流程:
- Google 会在用户的浏览器中打开您的授权端点。通过 如果用户尚未登录,则可以登录,并且授予 Google 访问 通过您的 API 访问其数据(如果尚未授予权限)。
- 您的服务会创建一个访问令牌并将其返回给 通过使用访问令牌将用户的浏览器重定向回 Google, 附件。
- Google 调用您的服务的 API,并使用 。您的服务会验证访问令牌是否向 Google 授予 访问 API 的授权,然后完成 API 调用。
处理授权请求
当您的 Action 需要通过 OAuth 2.0 隐式流程执行账号关联时, Google 会通过包含以下内容的请求将用户发送到您的授权端点: 以下参数:
| 授权端点参数 | |
|---|---|
client_id |
您分配给 Google 的客户 ID。 |
redirect_uri |
此请求的响应发送到的网址。 |
state |
将一个在 重定向 URI。 |
response_type |
要在响应中返回的值的类型。对于 OAuth 2.0 隐式
则响应类型始终为 token。 |
例如,如果您的授权端点可通过 https://myservice.example.com/auth 访问,
请求可能如下所示:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
为了让授权端点能够处理登录请求,请执行以下步骤:
验证
client_id和redirect_uri值, 防止向意外或配置错误的客户端应用授予访问权限:- 确认
client_id是否与您的客户端 ID 匹配 分配给 Google。 - 确认
redirect_uri指定的网址 参数的格式如下:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
- 确认
检查用户是否已登录您的服务。如果用户未登录 中,完成服务的登录或注册流程。
生成 Google 将用于访问您的 API 的访问令牌。通过 访问令牌可以是任何字符串值,但必须唯一地表示 令牌对应的用户和客户端,且不得被猜到。
发送 HTTP 响应,将用户浏览器重定向到相应网址 由
redirect_uri参数指定。添加所有 以下参数:access_token:您刚刚生成的访问令牌token_type:字符串bearerstate:原始状态的未修改状态值 请求 以下是生成的网址示例:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Google 的 OAuth 2.0 重定向处理程序将收到访问令牌并确认
state 值没有更改。在 Google 获得
访问令牌,则 Google 会将该令牌附加到后续调用
作为 AppRequest 的一部分添加到您的 Action。
为身份验证流程设计语音界面
检查用户是否已通过验证,并启动账号关联流程
- 在 Actions 控制台中打开您的 Actions Builder 项目。
- 创建新场景以在您的 Action 中启动账号关联:
- 点击场景。
- 点击添加 (+) 图标以添加新场景。
- 在新创建的场景中,点击条件的添加 add 图标。
- 添加一个条件,用于检查与对话关联的用户是否为已验证的用户。如果检查失败,您的 Action 将无法在对话期间执行账号关联,并且应回退到提供无需账号关联的功能。
- 在条件下的
Enter new expression字段中,输入以下逻辑:user.verificationStatus != "VERIFIED" - 在过渡下,选择不需要关联账号的场景,或选择仅限访客使用的功能的入口点场景。
- 在条件下的
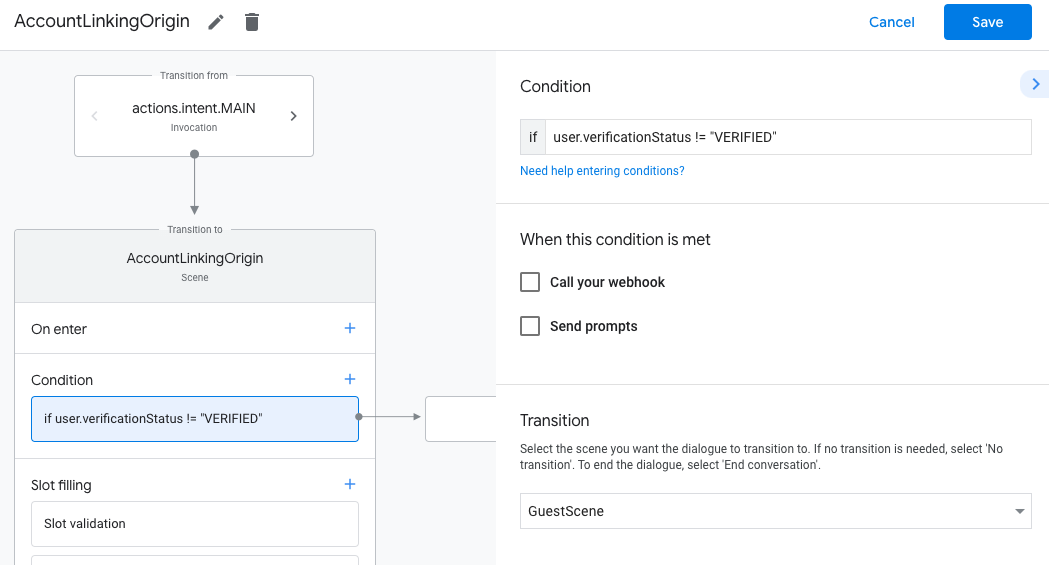
- 点击条件对应的添加 add 图标。
- 添加一个条件,以便在用户没有关联身份时触发账号关联流程。
- 在条件下的
Enter new expression字段中,输入以下逻辑:user.verificationStatus == "VERIFIED" - 在过渡下,选择账号关联系统场景。
- 点击保存。
- 在条件下的
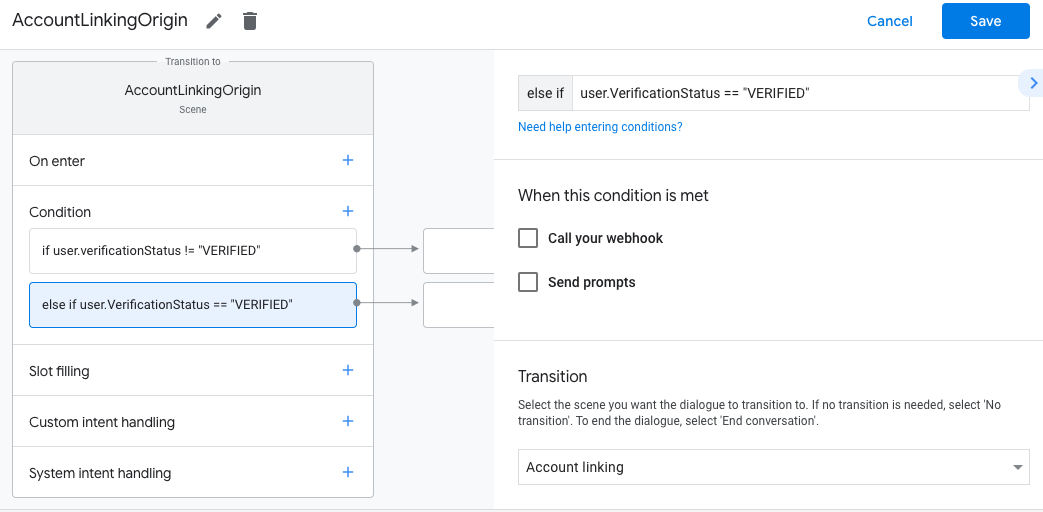
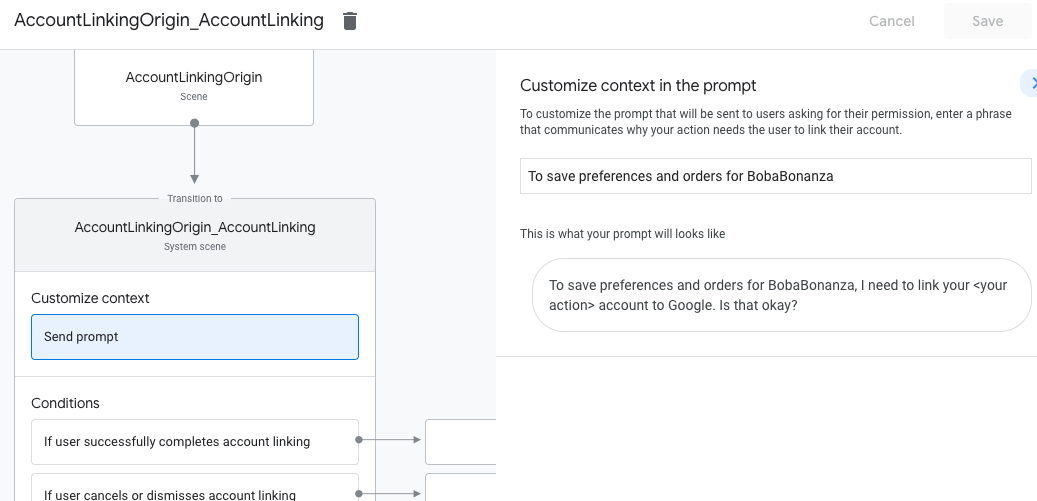
保存后,系统会在您的项目中添加一个名为 <SceneName>_AccountLinking 的新账号关联系统场景。
自定义账号关联场景
- 在场景下,选择账号关联系统场景。
- 点击发送提示,然后添加简短的句子,向用户说明该操作需要访问其身份信息的原因(例如“保存您的偏好设置”)。
- 点击保存。
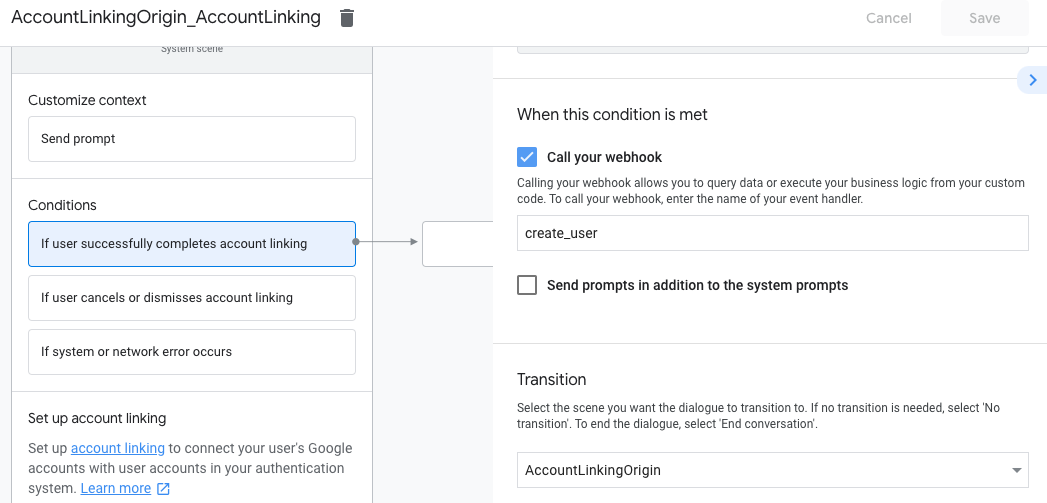
- 在条件下,点击如果用户成功完成账号关联。
- 配置用户同意关联账号后,流程应如何继续。 例如,调用网络钩子来处理所需的任何自定义业务逻辑,然后转换回原始场景。
- 点击保存。
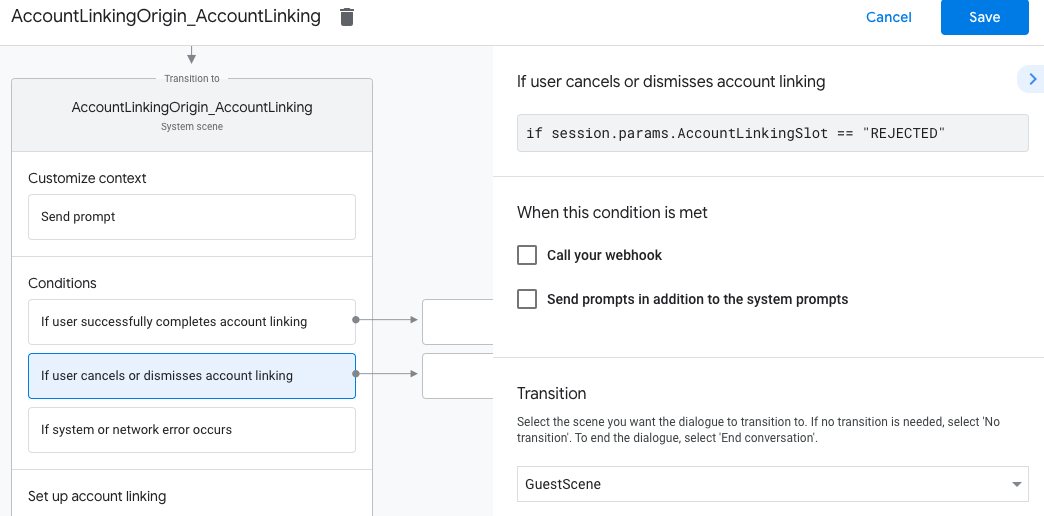
- 在条件下,点击如果用户取消或关闭账号关联。
- 配置用户不同意关联账号时流程应如何继续。例如,发送确认消息并重定向到提供不需要关联账号的功能的场景。
- 点击保存。
- 在条件下,点击如果发生系统或网络错误。
- 配置在因系统或网络错误而无法完成账号关联流程时,流程应如何继续。 例如,发送确认消息并重定向到提供不需要关联账号的功能的场景。
- 点击保存。
处理数据访问请求
如果辅助功能请求包含访问令牌,请先检查该访问令牌是否有效(未过期),然后从数据库中检索关联的用户账号。