Page Summary
-
Apps requesting sensitive or restricted Google API scopes to access consumer data require additional verification and potentially a security assessment.
-
Restricted scopes provide wide access to Google user data and require a scope verification process unless the app qualifies for an exception.
-
Understanding and reviewing the scopes your app uses, ensuring minimal necessary access, and accurately declaring scopes in the Cloud Console are crucial steps for verification.
-
Apps accessing restricted data from or through a third-party server must undergo an annual security assessment by a Google-approved third party.
-
Exceptions to verification requirements include personal use, development/testing/staging environments, service-owned data only, internal use within an organization, and domain-wide installation.
Certain Google APIs (the ones that accept Sensitive or Restricted scopes) have requirements for apps seeking permission to access consumer data. These additional requirements for restricted scopes require an app to demonstrate that they're a permitted application type and to submit to additional reviews, which include a possible security assessment.
The applicability of restricted scopes within an API depends mostly on the degree of access required to provide a relevant feature in your app: read-only, write-only, read and write, etc.
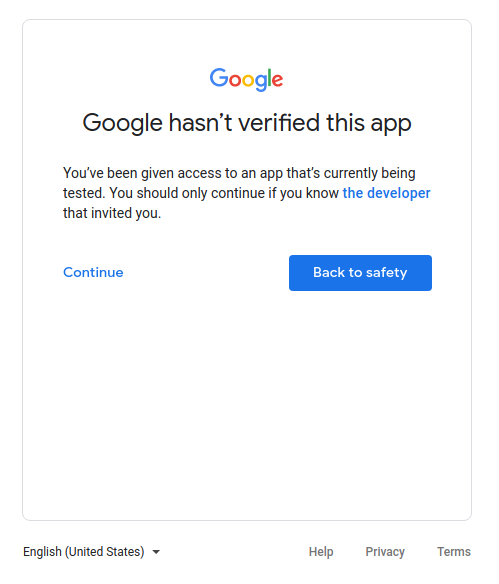
When you use OAuth 2.0 to get permission from a Google Account to access this data, you use strings called scopes to specify the type of data you want to access and how much access you need. If your app requests sensitive or restricted scopes, you need to complete the verification process unless your app's use qualifies for an exception.
Restricted scopes are fewer in number compared to sensitive scopes. The Verification OAuth API Verification FAQ contains the current list of Sensitive and Restricted scopes. These scopes provide wide access to Google user data and require you to go through a scope verification process before you request the scopes from any Google Account. For information on this requirement, see Google API Services User Data Policy and Additional requirements for specific API scopes or the product specific Google Developer page. If you store or transmit restricted scope data on servers, then you need to complete a security assessment.
Understand restricted scopes
If your app requests any restricted scopes and doesn't qualify for an exception, you need to satisfy the Additional requirements for specific API scopes of the Google API Services User Data Policy, or product specific requirements on the product's Google Developer page, which requires a more extensive review process.
Understand your scope use
- Review the scopes your app uses or you want to use. To find your existing scope usage, examine your app's source code for any scopes sent with authorization requests.
- Determine that each requested scope is necessary for your app feature's intended actions and uses the least privilege necessary to provide the feature. A Google API typically has reference documentation on the product's Google Developer page for its endpoints that includes the scope required to call the endpoint or specific properties within. For more information about the necessary scopes of access for the API endpoints that your app calls, read the reference documentation of those endpoints. For example, for an app that only uses Gmail APIs to occasionally send emails on a user's behalf, don't request the scope that provides full access to the user's email data.
- Data that you receive from a Google API must only be used in compliance with the policies of the API and in the way that you represent to your users in your app's actions and in your privacy policy.
- Reference the API documentation to learn more about each scope, including its potential sensitive or restricted status.
- Declare all scopes used by your app in the Cloud Console's Data Access page. Scopes you specify are grouped into sensitive or restricted categories to highlight any additional verification that's required.
- Find the best scope that matches the data used by your integration, understand its use, reconfirm that everything still works in a testing environment, and then prepare to submit for verification.
Be sure to account for the time needed to complete verification into your launch plan for your app or any new features that require a new scope. One of these additional requirements occurs if the app accesses or has the capability to access Google user data from or through a server. In these cases, the system must undergo an annual security assessment from an independent, third-party assessor that's approved by Google. For this reason, the restricted scopes verification process can potentially take several weeks to complete. Note that all apps must complete the brand verification step first, which typically takes 2-3 business days, if branding information has changed since the last approved OAuth consent screen verification.
Permitted application types
Certain application types can access restricted scopes for each product. You can find the application types on the product-specific Google Developer Page (for example, the Gmail API Policy).
It's your responsibility to understand and determine your app type. However, if you're truly unsure of your app's application type, you can select no options for the What features will you use? question when you submit the app for verification. The Google API's verification team will then determine the application type.
Security assessment
Every app that requests access to Google users' restricted data and has the ability to access data from or through a third-party server must go through a security assessment from Google-empanelled security assessors. This assessment helps keep Google users' data safe by verifying that all apps that access Google user data demonstrate the capability to handle data securely and to delete user data upon a user's request.
To standardize our security assessment we utilize the App Defense Alliance and the cloud application security assessment framework (CASA).
As mentioned previously, to keep access to any verified restricted scopes, apps must be reverified for compliance and complete a security assessment at least every 12 months after your assessor's Letter of Assessment (LOA) approval date. If your app adds a new restricted scope, your app might need to be reassessed to cover the additional scope if it wasn't included in a prior security assessment.
The Google review team emails you when it's time to recertify your app. To make sure that the correct members of your team are notified of this annual enforcement, associate additional Google Accounts with your Cloud Console project as an Owner or an Editor. It also helps to keep up-to-date the user support and developer contact emails that are specified in the Google Cloud Console OAuth Branding page.
Steps to prepare for verification
All apps that use Google APIs to request access to data must perform the following steps to complete brand verification:
- Confirm that your app doesn't fall under any of the use cases in the Exceptions to verification requirements section.
- Ensure that your app complies with the branding requirements of the associated APIs or product. For example, see the branding guidelines for Google Sign-In scopes.
- Verify ownership of your project's authorized domains within the Google Search Console. Use a Google Account that's associated with your API Console project as an Owner or an Editor.
- Make sure all branding information on the OAuth consent screen, such as the app name, support email, home page URI, privacy policy URI, etc., accurately represents the app's identity.
Application home page requirements
Make sure that your home page meets the following requirements:
- Your home page must be publicly accessible, and not just accessible to your site's logged-in users.
- The relevance of your home page to the app that's under review must be clear.
- Links to your app's listing on the Google Play Store or its Facebook page aren't considered valid application home pages.
Application privacy policy link requirements
Make sure that your app's privacy policy meets the following requirements:
- The privacy policy must be visible to users, hosted within the same domain as your application's home page, and linked to on the OAuth consent screen of the Google API Console. Note that the home page must include a description of the app's functionality, as well as links to the privacy policy and optional terms of service.
- The privacy policy must disclose the manner in which your application accesses, uses, stores, or shares Google user data. The privacy policy must comply with the Google API Services User Data Policy and the Limited Use requirements for restricted scopes. You must limit your use of Google user data to the practices that your published privacy policy discloses.
- Review example cases of privacy policies that don't meet the Limited Use requirements.
How to submit your app for verification
A Google Cloud Console project organizes all of your Cloud Console resources. A project consists of a set of associated Google Accounts that have permission to perform project operations, a set of enabled APIs, and billing, authentication, and monitoring settings for those APIs. For example, a project can contain one or more OAuth clients, configure APIs for use by those clients, and configure an OAuth consent screen that's shown to users before they authorize access to your app.
If any of your OAuth clients aren't ready for production, we suggest that you delete them from the project that's requesting verification. You can do this in the Clients page.
To submit for verification, follow these steps:
- Ensure your app complies with the Google APIs Terms of Service, and the Google API Services User Data Policy.
- Keep the owner and editor roles of your project's associated accounts current, as well as your OAuth consent screen's user support email and developer contact information, in your Cloud Console. This ensures that the correct members of your team are notified of any new requirements.
- Go to the Cloud Console OAuth Verification Center.
- Click the Project selector button.
-
On the Select from dialog that appears, select your project. If you can't find your project but you know your project ID, you can construct a URL in your browser in the following format:
https://console.developers.google.com/auth/branding?project=[PROJECT_ID]
Replace [PROJECT_ID] with the project ID you want to use.
- Select the Edit App button.
- Enter the necessary information on the OAuth consent screen page, and then select the Save and continue button.
- Use the Add or remove scopes button to declare all scopes requested by your app. An initial set of scopes that are necessary for Google Sign-In are pre-filled in the Non-sensitive scopes section. Added scopes are classified as non-sensitive, sensitive, or restricted.
- Provide up to three links to any relevant documentation for related features in your app.
-
Provide any additional information that's requested about your app in the subsequent steps.
- Ensure your app complies with the Additional requirements for specific API scopes, which includes undergoing an annual security assessment if your app accesses restricted scope Google users' data from or through a third-party server.
- Ensure your app is one of the allowed types specified in the Limited Use section of the Additional requirements for specific API scopes page.
- If your app is a task automation platform, your demonstration video must showcase how multiple API workflows are created and automated, and in which directions user data flows.
-
Prepare a video that fully demonstrates how a user initiates and grants access to the requested scopes and shows, in detail, the usage of the granted sensitive and restricted scopes in the app. Upload the video to YouTube Studio and set Visibility as Unlisted. You need to provide a link to the demonstration video in the YouTube link field.
- Show the OAuth grant process that users will experience, in English. This includes the consent flow and, if you use Google Sign-In, the sign-in flow.
- Show that the OAuth consent screen correctly displays the App Name.
- Show that the browser address bar of the OAuth consent screen correctly includes your app's OAuth client ID.
- To show how the data will be used, demonstrate the functionality that's enabled by each sensitive and restricted scope that you request.
- If you use multiple clients, and therefore have multiple OAuth client IDs, show how the data is accessed on each OAuth client.
- Select your permitted application type from the "What features will you use?" list.
- Describe how you will use the restricted scopes in your app and why more limited scopes aren't sufficient.
- If the app configuration you provide requires verification, you have the opportunity to submit the app for verification. Fill out the required fields and then click Submit to start the verification process.
After you submit your app, Google's Trust & Safety team follows up by email with any additional information they need or steps you must complete. Check your email addresses in the Developer contact information section and the support email of your OAuth consent screen for requests for additional information. You can also view your project's OAuth consent screen page to confirm your project's current review status, including whether the review process is paused while we wait for your response.
Exceptions to verification requirements
If your app is going to be used in any of the scenarios described in the following sections, you don't need to submit it for review.
Personal use
One use case is if you are the only user of your app or if your app is used by only a few users, all of whom are known personally to you. You and your limited number of users might be comfortable with advancing through the unverified app screen and granting your personal accounts access to your app.
Projects used in Development, Testing, or Staging tiers
In order to comply with Google OAuth 2.0 Policies, we recommend that you have different projects for testing and production environments. We recommend that you only submit your app for verification if you want to make your app available to any user with a Google Account. Therefore, if your app is in the development, testing, or staging phases, verification isn't required.
If your app is in the development or testing phases, you can leave the Publishing Status in the default setting of Testing. This setting means that your app is still in development and is only available to users you add to the list of test users. You must manage the list of Google Accounts that are involved in the development or testing of your app.
Service-owned data only
If your app uses a service account to access only its own data, and it doesn't access any user data (linked to a Google Account), then you don't need to submit for verification.
To understand what service accounts are, see Service accounts in Google Cloud's documentation. For instructions on how to use a service account, see Using OAuth 2.0 for server to server applications.
Internal use only
This means the app is used only by people in your Google Workspace or Cloud Identity organization. The project must be owned by the organization, and its OAuth consent screen needs to be configured for an Internal user type. In this case, your app might need approval from an organization administrator. For more information, see Additional considerations for Google Workspace.
- Learn more about public and internal applications.
- Learn how to mark your app as internal in the FAQ How can I mark my app as internal-only?
Domain-wide installation
If you plan for your app to only target users of a Google Workspace or Cloud Identity organization and always use domain-wide installation, then your app won't require brand verification. However, if your app utilizes restricted or sensitive scopes, app verification is required. This is because a domain-wide installation lets a domain administrator grant third-party and internal applications access to your users' data. Organization administrators are the only accounts that can add the app to an allowlist for use within their domains.
Learn how to make your app a Domain-Wide Install in the FAQ My application has users with enterprise accounts from another Google Workspace Domain.