계정은 업계 표준 OAuth 2.0 암시적 흐름 및 승인 코드 흐름을 사용하여 연결됩니다. 서비스가 OAuth 2.0을 준수하는 승인 및 토큰 교환 엔드포인트를 지원해야 합니다.
암시적 흐름에서는 Google이 사용자의 브라우저에서 승인 엔드포인트를 엽니다. 로그인에 성공하면 장기 액세스 토큰을 Google에 반환합니다. 이제 Google에서 전송하는 모든 요청에 이 액세스 토큰이 포함됩니다.
승인 코드 흐름에는 두 개의 엔드포인트가 필요합니다.
아직 로그인하지 않은 사용자에게 로그인 UI를 표시하는 승인 엔드포인트입니다. 승인 엔드포인트는 요청된 액세스에 대한 사용자의 동의를 기록하기 위해 단기 승인 코드도 만듭니다.
두 가지 유형의 교환을 담당하는 토큰 교환 엔드포인트:
- 승인 코드를 사용 기간이 긴 갱신 토큰 및 사용 기간이 짧은 액세스 토큰으로 교환합니다. 이 교환은 사용자가 계정 연결 흐름을 진행할 때 발생합니다.
- 장기 갱신 토큰을 단기 액세스 토큰으로 교환합니다. 이 교환은 만료된 액세스 토큰으로 인해 Google에 새 액세스 토큰이 필요할 때 발생합니다.
OAuth 2.0 흐름 선택
암시적 흐름은 구현하기가 더 간단하지만 암시적 흐름에서 발급된 액세스 토큰은 만료되지 않도록 하는 것이 좋습니다. 이는 암시적 흐름으로 토큰이 만료된 후 사용자가 계정을 다시 연결해야 하기 때문입니다. 보안상의 이유로 토큰 만료가 필요한 경우에는 승인 코드 흐름을 대신 사용하는 것이 좋습니다.
디자인 가이드라인
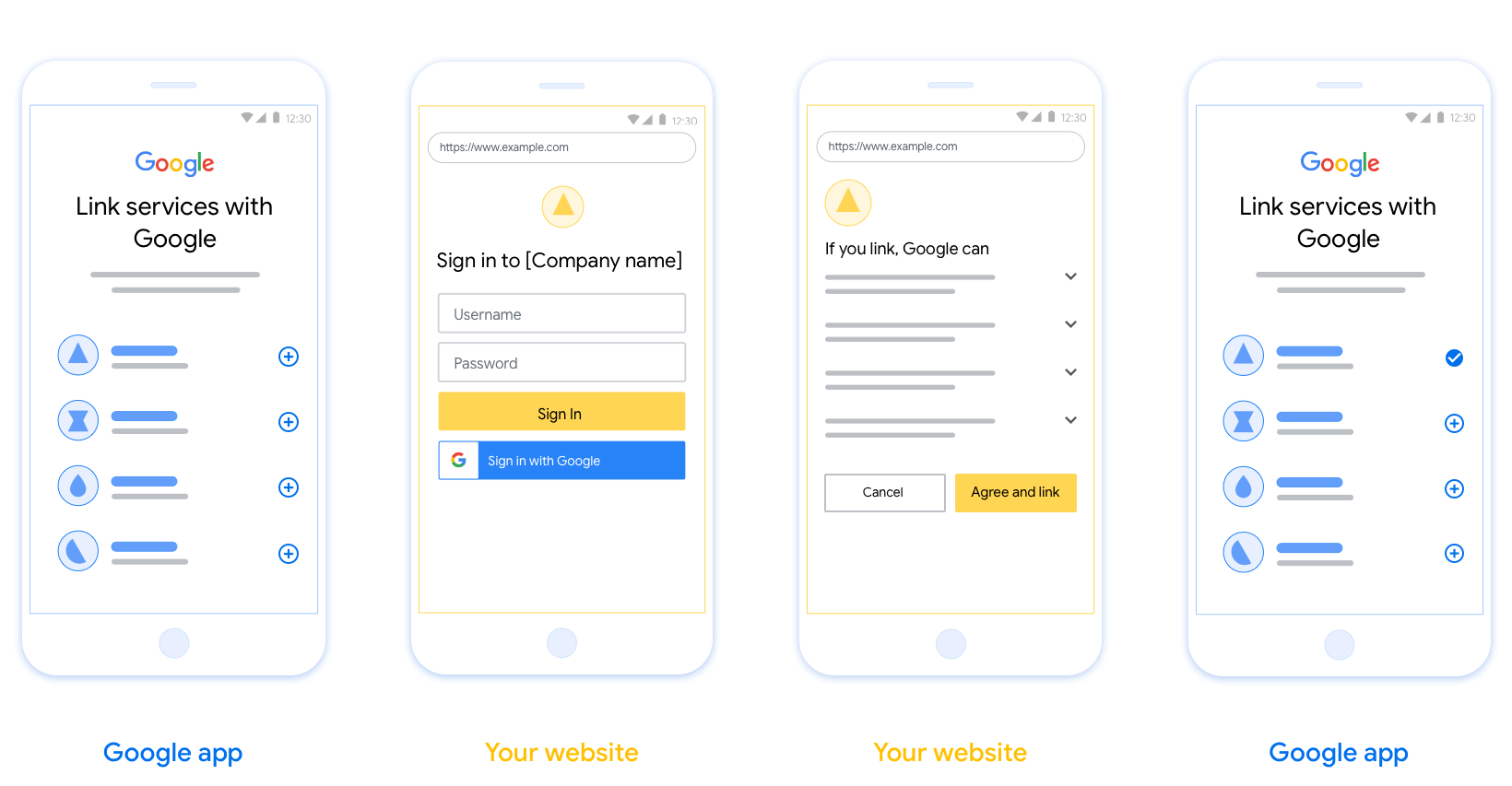
이 섹션에서는 OAuth 연결 흐름을 위해 호스팅하는 사용자 화면에 대한 디자인 요구사항과 권장사항을 설명합니다. Google 앱에서 호출하면 플랫폼에서 사용자에게 Google 로그인 페이지와 계정 연결 동의 화면을 표시합니다. 사용자가 계정 연결에 동의하면 Google 앱으로 다시 리디렉션됩니다.
요구사항
- 사용자의 계정이 Google Home 또는 Google 어시스턴트와 같은 특정 Google 제품이 아닌 Google에 연결된다고 안내해야 합니다.
권장사항
다음을 수행하는 것이 좋습니다.
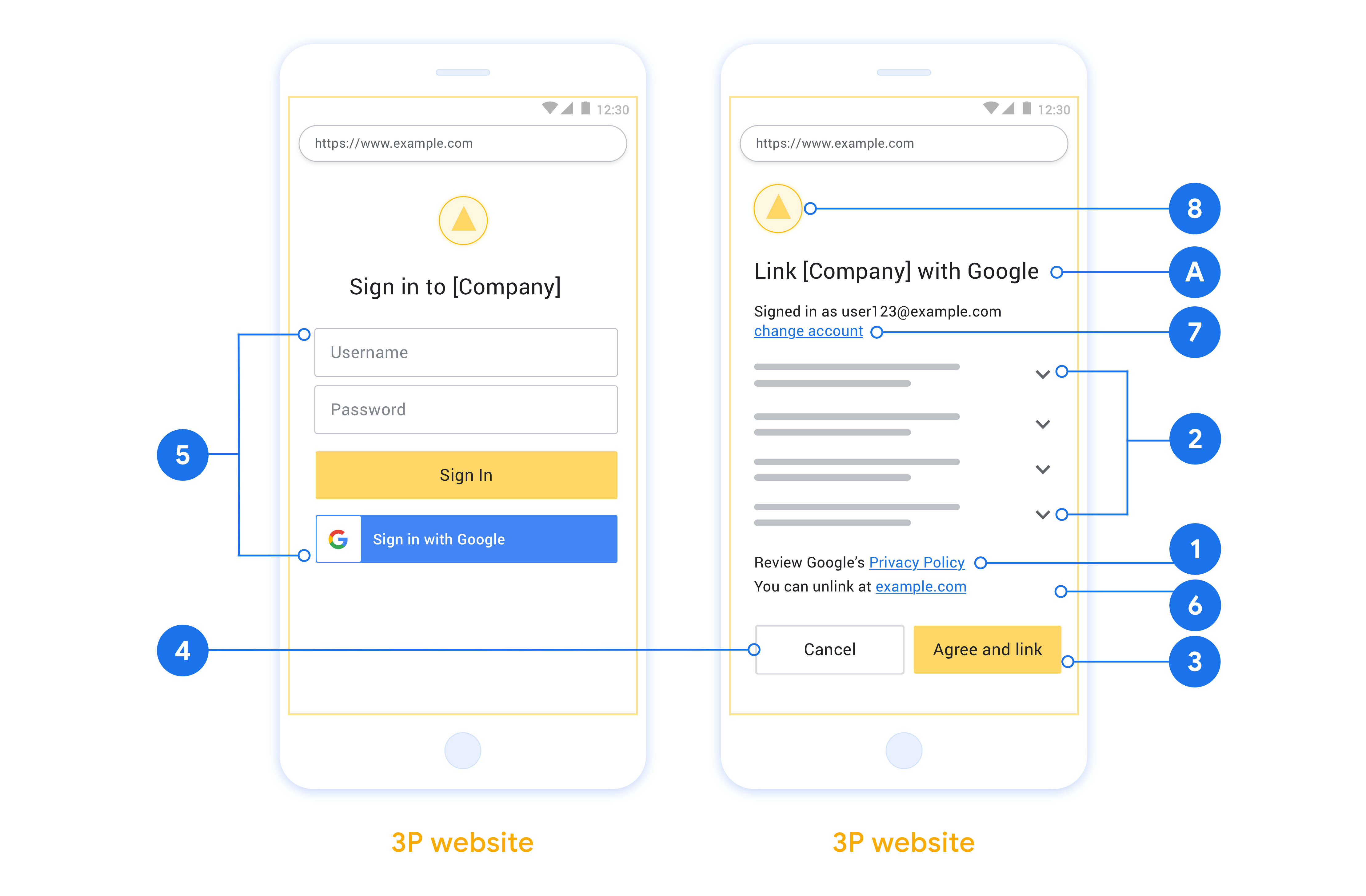
Google 개인정보처리방침을 표시합니다. 동의 화면에 Google 개인정보처리방침 링크를 포함합니다.
공유할 데이터 Google에서 필요로 하는 데이터와 그 이유를 사용자에게 명확하고 간결한 언어로 전달하세요.
명확한 클릭 유도 문구 '동의 및 연결'과 같은 명확한 클릭 유도 문구를 동의 화면에 표시합니다. 이는 사용자가 계정을 연결하기 위해 Google과 공유해야 하는 데이터를 이해해야 하기 때문입니다.
취소 기능 사용자가 연결하지 않기로 선택한 경우 뒤로 돌아가거나 취소할 수 있는 방법을 제공합니다.
명확한 로그인 절차. 사용자에게 사용자 이름 및 비밀번호 입력란이나 Google 계정으로 로그인과 같이 Google 계정에 로그인하는 명확한 방법이 제공되어야 합니다.
연결 해제 기능. 사용자가 연결을 해제할 수 있는 메커니즘(예: 플랫폼의 계정 설정 URL)을 제공합니다. 또는 사용자가 연결된 계정을 관리할 수 있는 Google 계정 링크를 포함할 수 있습니다.
사용자 계정을 변경할 수 있는 기능 사용자가 계정을 전환할 수 있는 방법을 제안합니다. 이는 사용자가 여러 계정을 사용하는 경향이 있는 경우에 특히 유용합니다.
- 사용자가 계정을 전환하려면 동의 화면을 닫아야 하는 경우 사용자가 OAuth 연결 및 암시적 흐름으로 원하는 계정에 로그인할 수 있도록 복구 가능한 오류를 Google에 전송합니다.
로고를 포함합니다. 동의 화면에 회사 로고를 표시합니다. 스타일 가이드라인에 따라 로고를 배치합니다. Google 로고도 표시하려면 로고 및 상표를 참고하세요.
프로젝트 만들기
계정 연결을 사용할 프로젝트를 만들려면 다음 단계를 따르세요.
- 프로젝트 만들기를 클릭합니다.
- 이름을 입력하거나 생성된 추천을 수락합니다.
- 나머지 필드를 확인하거나 수정합니다.
- 만들기를 클릭합니다.
프로젝트 ID를 확인하려면 다음 단계를 따르세요.
- 방문 페이지의 표에서 프로젝트를 찾습니다. 프로젝트 ID는 ID 열에 표시됩니다.
OAuth 동의 화면 구성
Google 계정 연결 프로세스에는 사용자에게 데이터 액세스를 요청하는 애플리케이션, 요청하는 데이터의 종류, 적용되는 약관을 알려주는 동의 화면이 포함됩니다. Google API 클라이언트 ID를 생성하기 전에 OAuth 동의 화면을 구성해야 합니다.
- Google API 콘솔의 OAuth 동의 화면 페이지를 엽니다.
- 메시지가 표시되면 방금 만든 프로젝트를 선택합니다.
'OAuth 동의 화면' 페이지에서 양식을 작성하고 '저장' 버튼을 클릭합니다.
애플리케이션 이름: 동의를 요청하는 애플리케이션의 이름입니다. 이름은 애플리케이션을 정확하게 반영해야 하며 사용자가 다른 곳에서 보는 애플리케이션 이름과 일치해야 합니다. 애플리케이션 이름은 계정 연결 동의 화면에 표시됩니다.
애플리케이션 로고: 사용자가 앱을 인식하는 데 도움이 되는 동의 화면의 이미지입니다. 로고는 계정 연결 동의 화면과 계정 설정에 표시됩니다.
지원 이메일: 사용자가 동의에 대해 문의할 수 있습니다.
Google API 범위: 범위를 사용하면 애플리케이션이 사용자의 비공개 Google 데이터에 액세스할 수 있습니다. Google 계정 연결 사용 사례의 경우 기본 범위 (이메일, 프로필, openid)로 충분하며 민감한 범위를 추가할 필요가 없습니다. 일반적으로 액세스가 필요한 시점에 미리 요청하는 대신 점진적으로 범위를 요청하는 것이 좋습니다. 자세히 알아보기
승인된 도메인: 나와 내 사용자를 보호하기 위해 Google에서는 OAuth를 사용하여 인증하는 애플리케이션만 승인된 도메인을 사용할 수 있도록 허용합니다. 애플리케이션의 링크는 승인된 도메인에서 호스팅되어야 합니다. 자세히 알아보기
애플리케이션 홈페이지 링크: 애플리케이션의 홈페이지입니다. 승인된 도메인에서 호스팅해야 합니다.
애플리케이션 개인정보처리방침 링크: Google 계정 연결 동의 화면에 표시됩니다. 승인된 도메인에서 호스팅해야 합니다.
애플리케이션 서비스 약관 링크 (선택사항): 승인된 도메인에서 호스팅되어야 합니다.
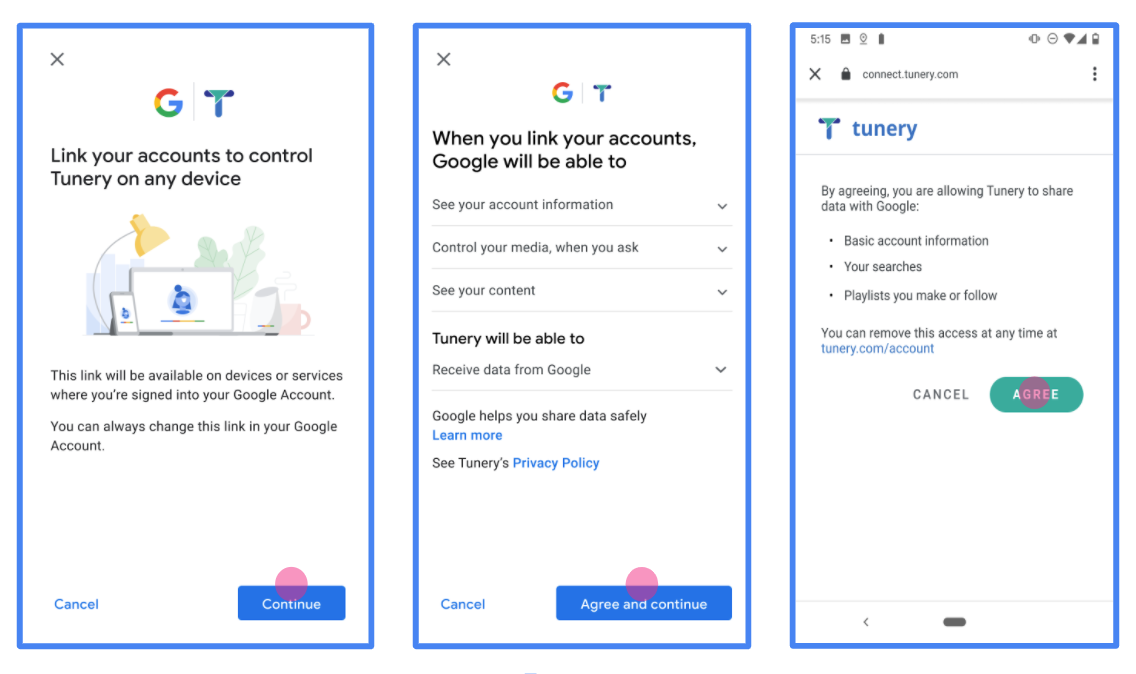
그림 1. 가상 애플리케이션 Tunery의 Google 계정 연결 동의 화면
'인증 상태'를 확인합니다. 애플리케이션에 인증이 필요한 경우 '인증을 위해 제출' 버튼을 클릭하여 인증을 위해 애플리케이션을 제출합니다. 자세한 내용은 OAuth 인증 요구사항을 참고하세요.
OAuth 서버 구현
OAuth 2.0 암시적 흐름을 지원하기 위해 서비스 승인 사용할 수 있습니다 이 엔드포인트는 인증과 데이터 액세스에 대한 사용자의 동의 받기 승인 엔드포인트 아직 로그인하지 않은 사용자에게 로그인 UI를 표시하고 액세스할 수 있도록 합니다.
Google 애플리케이션이 서비스의 승인된 API 중 하나를 호출해야 하는 경우 Google은 이 엔드포인트를 사용하여 사용자로부터 이러한 API를 호출할 권한을 얻습니다. 위임할 수 있습니다
Google에서 시작한 일반적인 OAuth 2.0 암시적 흐름 세션에는 다음 흐름을 따라 하세요.
- Google은 사용자의 브라우저에서 승인 엔드포인트를 엽니다. 이 사용자가 아직 로그인하지 않은 경우 로그인하고 Google에 다음 권한을 부여합니다. 아직 권한을 부여하지 않은 경우 API를 통해 데이터에 액세스할 수 있습니다.
- 서비스에서 액세스 토큰을 만들고 이를 Google 이렇게 하려면 사용자의 브라우저를 액세스 권한이 있는 Google로 다시 리디렉션합니다. 토큰입니다.
- Google은 서비스의 API를 호출하고 실행할 수 있습니다 서비스에서 액세스 토큰이 Google에 인증한 다음 API 호출을 완료합니다.
승인 요청 처리
Google 애플리케이션에서 OAuth 2.0을 통해 계정 연결을 수행해야 하는 경우 Google은 인증 엔드포인트로 사용자를 다음과 같은 매개변수를 포함합니다.
| 승인 엔드포인트 매개변수 | |
|---|---|
client_id |
Google에 할당한 클라이언트 ID입니다. |
redirect_uri |
이 요청에 대한 응답을 보낼 URL입니다. |
state |
정해진 기간에 변경되지 않고 Google에 다시 전달되는 리디렉션 URI를 사용할 수 있습니다. |
response_type |
응답에서 반환할 값의 유형입니다. OAuth 2.0 암시적
흐름에서 응답 유형은 항상 token입니다. |
user_locale |
Google 계정 언어 설정 RFC5646 콘텐츠를 사용자가 선호하는 언어로 현지화하는 데 사용되는 형식입니다. |
예를 들어 승인 엔드포인트를
https://myservice.example.com/auth인 경우 요청은 다음과 같을 수 있습니다.
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token&user_locale=LOCALE
승인 엔드포인트가 로그인 요청을 처리하도록 하려면 다음을 수행합니다. 단계:
다음과 같이
client_id및redirect_uri값을 확인합니다. 의도하지 않았거나 잘못 구성된 클라이언트 앱에 액세스 권한을 부여하지 않도록 합니다.client_id가 등록된 클라이언트 ID와 일치하는지 확인합니다. 확인할 수 있습니다redirect_uri에서 지정한 URL인지 확인합니다. 매개변수의 형식은 다음과 같습니다.https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID https://oauth-redirect-sandbox.googleusercontent.com/r/YOUR_PROJECT_ID
사용자가 서비스에 로그인했는지 확인합니다. 사용자가 로그인하지 않은 경우 서비스의 로그인 또는 가입 절차를 완료합니다.
Google에서 API에 액세스하는 데 사용할 액세스 토큰을 생성합니다. 이 액세스 토큰은 임의의 문자열 값이 될 수 있지만 클라이언트와 클라이언트에게 전달하며 추측할 수 없어야 합니다.
사용자의 브라우저를 URL로 리디렉션하는 HTTP 응답 전송
redirect_uri매개변수로 지정됩니다. 다음을 모두 포함 다음 매개변수를 포함합니다.access_token: 방금 생성한 액세스 토큰입니다.token_type: 문자열bearerstate: 원본의 수정되지 않은 상태 값입니다. 요청
다음은 결과 URL의 예입니다.
https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Google의 OAuth 2.0 리디렉션 핸들러가 액세스 토큰을 수신하고
state 값이 변경되지 않았음을 확인합니다. Google이
Google에서 후속 호출에 토큰을 첨부합니다.
서비스 API에 연결할 수 있습니다
사용자 정보 요청 처리
userinfo 엔드포인트는 연결된 사용자에 대한 클레임을 반환하는 OAuth 2.0 보호 리소스입니다. 다음 사용 사례를 제외하고 userinfo 엔드포인트를 구현하고 호스팅하는 것은 선택사항입니다.
- Google 원탭을 사용한 연결된 계정 로그인
- AndroidTV의 원활한 구독
토큰 엔드포인트에서 액세스 토큰을 성공적으로 가져오면 Google은 사용자 정보 엔드포인트에 요청을 보내 연결된 사용자에 대한 기본 프로필 정보를 가져옵니다.
| 사용자 정보 엔드포인트 요청 헤더 | |
|---|---|
Authorization header |
Bearer 유형의 액세스 토큰입니다. |
예를 들어
https://myservice.example.com/userinfo인 경우 요청은 다음과 같을 수 있습니다.
GET /userinfo HTTP/1.1 Host: myservice.example.com Authorization: Bearer ACCESS_TOKEN
userinfo 엔드포인트에서 요청을 처리하려면 다음 단계를 수행합니다.
- 승인 헤더에서 액세스 토큰을 추출하고 액세스 토큰과 연결된 사용자의 정보를 반환합니다.
- 액세스 토큰이 유효하지 않은 경우
WWW-Authenticate응답 헤더를 사용하여 HTTP 401 승인되지 않은 오류를 반환합니다. 다음은 userinfo 오류 응답의 예입니다.HTTP/1.1 401 Unauthorized WWW-Authenticate: error="invalid_token", error_description="The Access Token expired"
액세스 토큰이 유효하면 HTTPS 본문에 다음 JSON 객체가 포함된 HTTP 200 응답을 반환합니다. 응답:
{ "sub": "USER_UUID", "email": "EMAIL_ADDRESS", "given_name": "FIRST_NAME", "family_name": "LAST_NAME", "name": "FULL_NAME", "picture": "PROFILE_PICTURE", }사용자 정보 엔드포인트 응답 sub시스템에서 사용자를 식별하는 고유 ID email사용자의 이메일 주소입니다. given_name선택사항: 사용자의 이름입니다. family_name선택사항: 사용자의 성. name선택사항: 사용자의 전체 이름입니다. picture선택사항: 사용자의 프로필 사진입니다.
구현 확인
OAuth 2.0 플레이그라운드 도구를 사용하여 구현을 검증할 수 있습니다.
도구에서 다음 단계를 수행합니다.
- 구성 을 클릭하여 OAuth 2.0 구성 창을 엽니다.
- OAuth 흐름 입력란에서 클라이언트 측을 선택합니다.
- OAuth 엔드포인트 필드에서 맞춤을 선택합니다.
- 해당 필드에 OAuth 2.0 엔드포인트와 Google에 할당한 클라이언트 ID를 지정합니다.
- 1단계 섹션에서 Google 범위를 선택하지 않습니다. 대신 이 필드를 비워 두거나 서버에 유효한 범위 (또는 OAuth 범위를 사용하지 않는 경우 임의의 문자열)를 입력합니다. 완료되면 API 승인을 클릭합니다.
- 2단계 및 3단계 섹션에서 OAuth 2.0 흐름을 진행하고 각 단계가 의도한 대로 작동하는지 확인합니다.
Google 계정 연결 데모 도구를 사용하여 구현을 확인할 수 있습니다.
도구에서 다음 단계를 수행합니다.
- Google 계정으로 로그인 버튼을 클릭합니다.
- 연결할 계정을 선택합니다.
- 서비스 ID를 입력합니다.
- 원하는 경우 액세스를 요청할 범위를 하나 이상 입력합니다.
- 데모 시작을 클릭합니다.
- 메시지가 표시되면 연결 요청에 동의하고 거부할 수 있음을 확인합니다.
- 플랫폼으로 리디렉션되는지 확인합니다.